🌐 Protocols & Ports Explained
1. What Are Protocols?
- Definition: Protocols are standardized rules that define how data is transmitted and received across networks.
- Types:
- TCP (Transmission Control Protocol): Connection‑oriented, ensures reliable delivery.
- UDP (User Datagram Protocol): Connectionless, faster but less reliable.
- Other examples: HTTP, HTTPS, FTP, SMTP, DNS, SNMP.
- Role: They act like languages — ensuring both sender and receiver understand each other.
2. What Are Ports?
- Definition: A port is a numeric identifier (0–65535) that specifies which application or service should handle incoming data.
- Analogy: Think of the IP address as a building, and ports as apartment numbers inside that building.
- Categories:
- Well‑known ports (0–1023): Reserved for standard services.
- Registered ports (1024–49151): Assigned to user or vendor applications.
- Dynamic/private ports (49152–65535): Temporary, used for client connections.
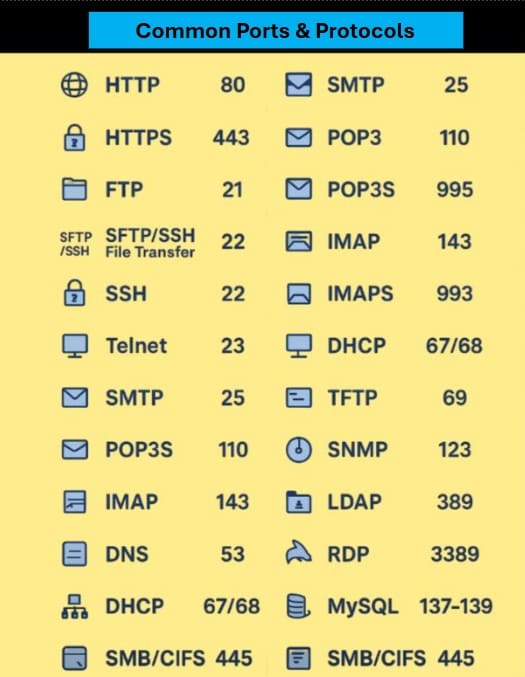
3. Common Protocols & Ports
| Protocol | Port | Transport | Use |
|---|---|---|---|
| HTTP | 80 | TCP | Web traffic (unencrypted) |
| HTTPS | 443 | TCP | Secure web traffic |
| FTP | 21 | TCP | File transfer |
| SMTP | 25 | TCP | Sending email |
| DNS | 53 | UDP/TCP | Domain name resolution |
| SSH | 22 | TCP | Secure remote login |
| Telnet | 23 | TCP | Remote login (insecure, legacy) |
| SNMP | 161 | UDP | Network management |
| NTP | 123 | UDP | Time synchronization |
4. How Protocols & Ports Work Together
- When you visit
https://example.com:- Browser uses HTTPS protocol.
- Data is sent to port 443 on the server.
- Server responds using the same protocol and port.
- This ensures the right application (web server) handles the request.
5. Security Considerations
- Open ports can be exploited if services are misconfigured.
- Firewalls control which ports are accessible.
- Best practice: Only keep necessary ports open, and secure protocols (HTTPS, SSH) should replace insecure ones (HTTP, Telnet).
✅ Summary:
- Protocols = rules of communication.
- Ports = numbered endpoints for services.
- Together, they ensure data flows to the correct application securely and efficiently.



Must log in before commenting!
Sign Up